Know the Threat
Before It Arrives
Cyber threats evolve faster than
any individual vessel can track.
CYTUR monitors the dark web, deep web, and global threat feeds
around the clock to proactively collect and analyze
threats targeting the maritime industry.
Generic CTI cannot cover
maritime-specific cyber threats
General-purpose cyber threat intelligence (CTI) services designed for land-based environments lack understanding of vessel-specific equipment and maritime communication protocols.
NMEA and AIS protocol vulnerabilities, leaked vessel access credentials, and targeted attacks on maritime equipment manufacturers are maritime-unique threats that generic CTI simply cannot cover.
— the core of proactive maritime defense
Threat Intelligence Solution
Threat Intelligence
Maritime-specific cyber threat intelligence platform
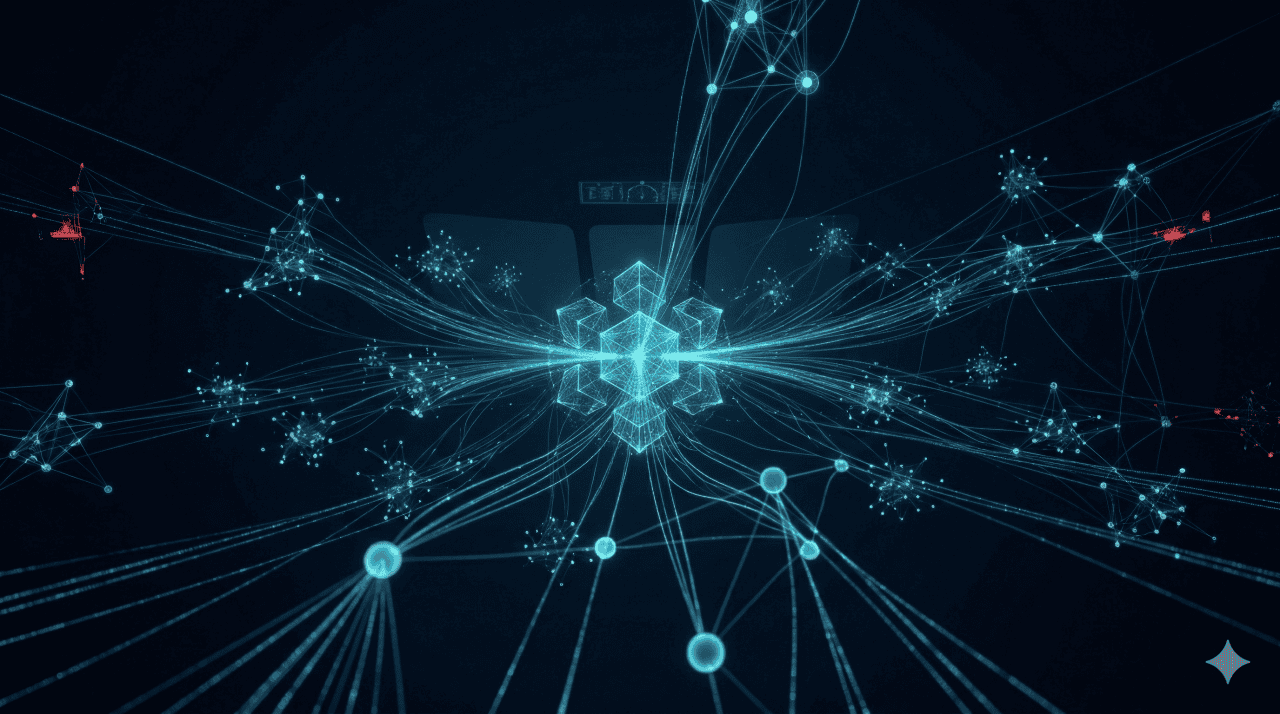
Real-Time Global Maritime Incident Radar
Collects cyber attack and incident data from maritime operations worldwide in real time and visualizes them on a global map.
24/7 Dark Web & Deep Web Monitoring
Continuously monitors hacker marketplaces (dark web) and encrypted channels to detect data leaks related to your shipping company.
Onboard Equipment Vulnerability Assessment
Analyzes security weaknesses and potential intrusion paths for critical devices installed onboard.
MG Integration — OT × TI Cross-Analysis
Cross-references external threat intelligence (TI) with internal vessel OT status to clearly distinguish between mechanical failures and external cyberattacks.
Threat Intelligence Operations Process
Threat Data Collection
Automatically collects maritime-targeted threat data 24/7 from the dark web, deep web, open sources, and global threat feeds.
Maritime-Specific Analysis & Classification
Analyzes collected data within the maritime domain context and classifies risk levels by shipping company, vessel, and equipment.
MG Integration & Cross-Analysis
Cross-references external threat intelligence with onboard OT status data to clearly distinguish failures from attacks and establish threat context.
Customized Alerts & Report Generation
Issues tailored threat alerts per shipping company and auto-generates IACS UR E26 threat analysis reports.
Expected Outcomes
not post-incident response
mandatory threat analysis reports
from equipment manufacturers to ship operators
Start Threat Intelligence
From dark web monitoring to customized threat briefings —
experience maritime-specialized CTI firsthand.