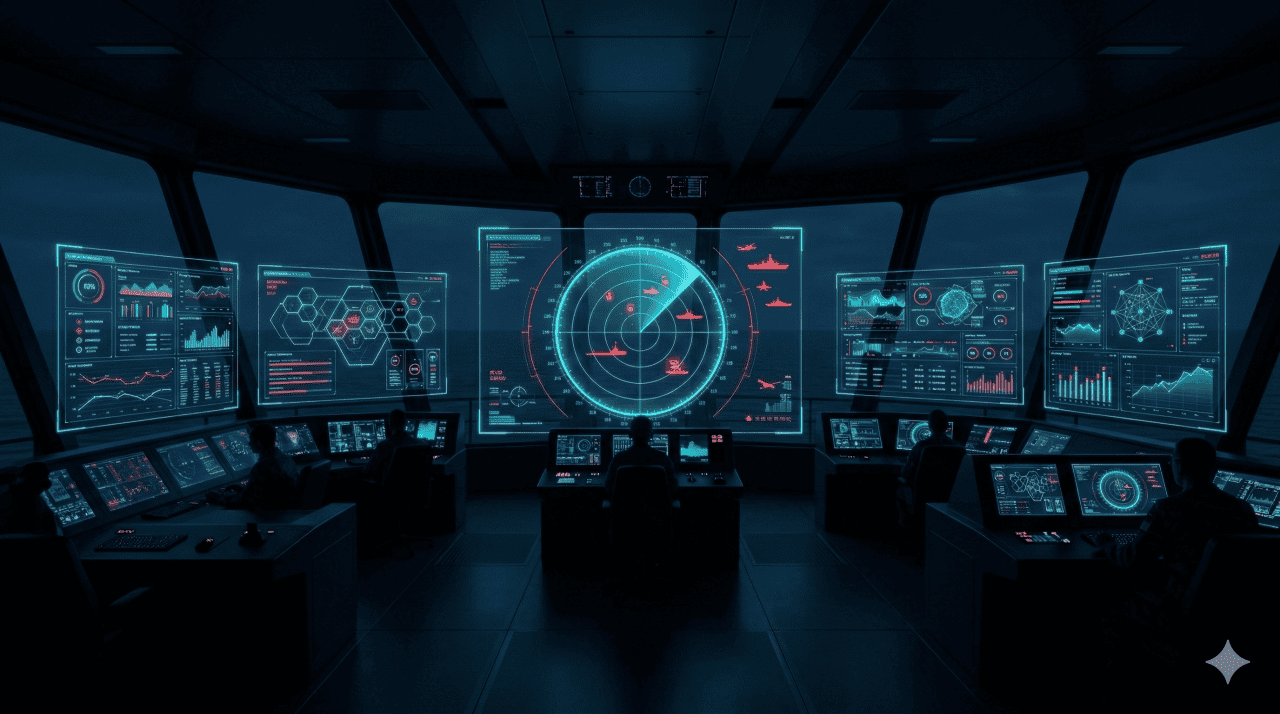
Cyber Defense That Never Stops
After Departure
A single undetected intrusion can compromise
navigation, propulsion, and cargo systems.
CYTUR detects threats in real time with vessel-specific AI,
integrating cyber deception defense and
AI-powered visual security into a unified command.
Once at sea, vessels face real-time cyber threats without IT support
As vessels digitize and connect to shore networks, previously isolated OT control systems are now exposed to external threats. The attack surface available to hackers has expanded to critical levels.
Conventional security equipment is prone to malfunction due to satellite communication latency and cannot interpret vessel-specific protocols like NMEA and AIS — missing critical threats or generating false positives.
cyberattack detection
— SD's real-time detection speed
Operate Phase Solutions
Maritime Guard
Intelligent integrated cyber resilience management platform
Aggregates and analyzes threat data from all onboard equipment and automates regulatory compliance workflows. An all-in-one platform integrating NS + TA + RM.
Ship Network Defense
Vessel-specific intrusion detection system
Analyzes vessel-specific protocols such as NMEA, Modbus, and AIS using AI to identify anomalous access in real time — threats invisible to conventional security tools.
Ship Honeypot
Cyber deception defense system
Deploys decoy systems that mimic real vessel systems within the onboard network to lure attackers and block access to actual critical systems.
Ship AI Vision Defender
AI video surveillance threat response solution
Detects adversarial attacks targeting AI-powered CCTV on autonomous vessels in real time and restores video to original quality.
Operate Phase Integrated Defense Process
Real-Time Network Surveillance
NS collects all onboard traffic while SD analyzes vessel-specific protocols with AI to detect anomalies in under one second.
Threat Deception & Isolation
SHIPPOT lures intruders into decoy systems, blocking access to actual critical systems and collecting attack patterns.
Unified Analysis & Correlation
TA integrates data from NS, SD, SHIPPOT, and TI to understand the full context of an attack beyond isolated events.
Risk Management & Regulatory Compliance
RM automatically logs threat response history and generates IACS UR E26/E27 compliant class submission reports.
Expected Outcomes
the golden time for cyberattack response
and reports for class certification
for complete vessel security visibility
Start Securing the Operate Phase
From real-time threat detection to automated class certification —
experience unified command and control firsthand.