VERIFY
CYTUR-SC®
Scanner
Vessel, Asset & Network Portable Scanner
A portable security integrity verification solution that automatically discovers all assets connected to complex vessel networks and performs deep analysis for hidden vulnerabilities. It identifies and classifies even undetectable shadow devices, objectively verifying the vessel's security posture.
Why You Need It
Why a Portable Security Scanner Is Essential
📋
Overcoming Manual Inspection Limitations
With the proliferation of smart vessels and rapidly increasing onboard equipment, manual inspections are not only extremely time-consuming and costly but inevitably create security blind spots due to data omissions.
📜
Mandatory Compliance with IACS UR E26/E27
Under IACS regulations mandatory since July 2024, all newbuilds must verify the security integrity of onboard critical systems (CBS) before delivery and submit results to classification societies. CYTUR-SC® automatically scans installed equipment to inspect vulnerabilities and configurations, generating objective technical evidence for the required 'field verification'.
Key Benefits
The Value CYTUR-SC® Delivers
01
Cost Reduction
Secure Operational Stability Through Proactive Defect Resolution
By identifying and resolving security defects before vessel delivery, dramatically reduces massive repair costs during actual operations and proactively prevents operational disruption risks.
02
Full Visibility
Complete Asset Discovery Including Hidden Shadow Devices
Conducts comprehensive surveys of all control systems under actual operational conditions, building a transparent management framework that includes devices missing from inventories and temporarily connected equipment.
03
Management Efficiency
Automated Real-Time Network Change Tracking
Manages frequent equipment additions and changes during sea trials through automated scanning instead of manual labor, tracking and controlling all network changes.
Core Features
Core Capabilities
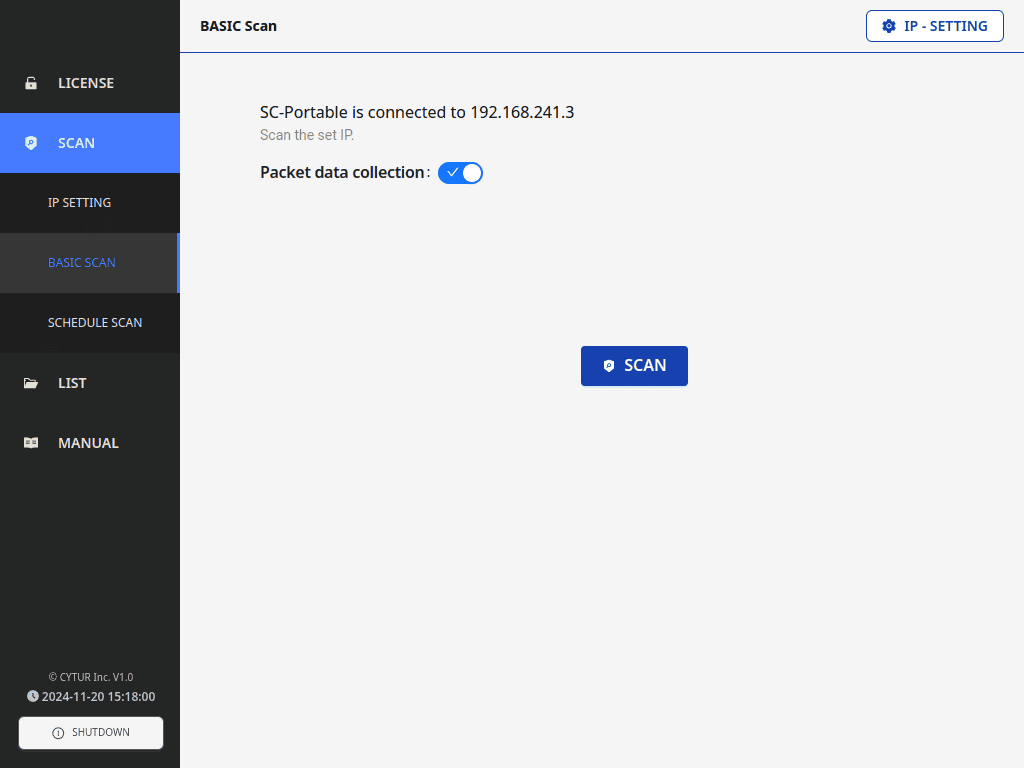
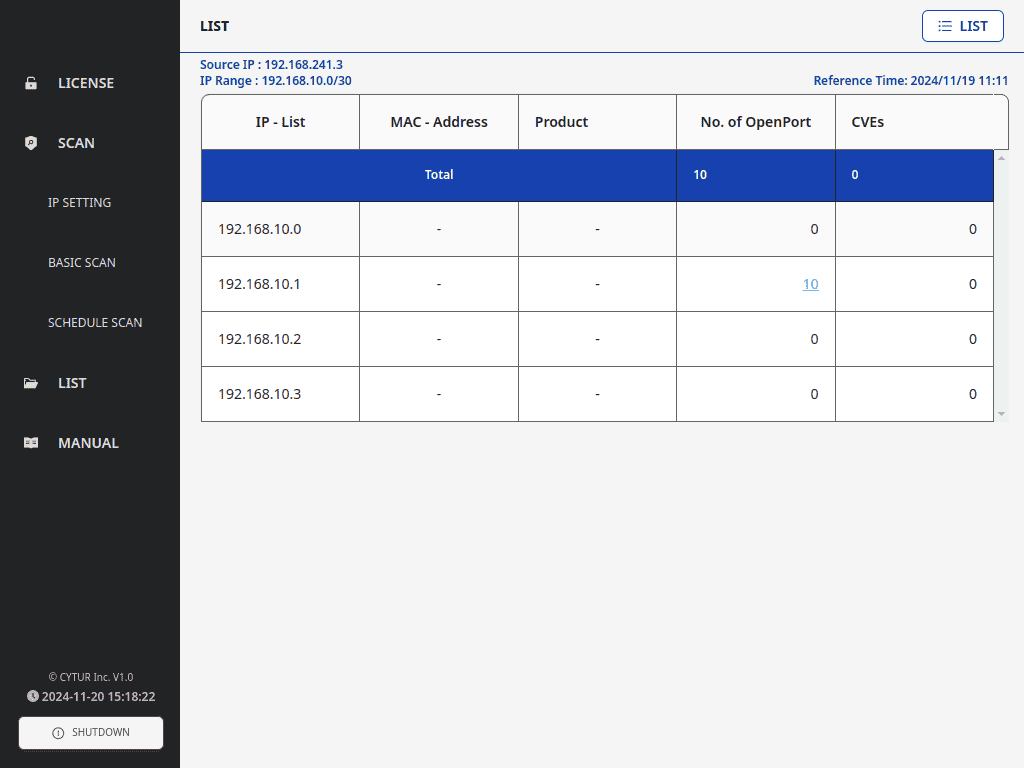
Fast & Accurate Vessel Equipment Discovery
Automated Asset Identification
Simply enter the network address to instantly discover all connected equipment (CBS). Automatically matches device names, manufacturers, and OS information without additional software installation, finding even hidden devices invisible to the naked eye to build a complete asset inventory.

24/7 Automated Security Scan Scheduling
Schedule-Based Automation
Schedule security scans at desired times. Even if equipment powers off and restarts, scans automatically resume according to schedule, maintaining continuous security status without data gaps throughout extended sea trial periods.
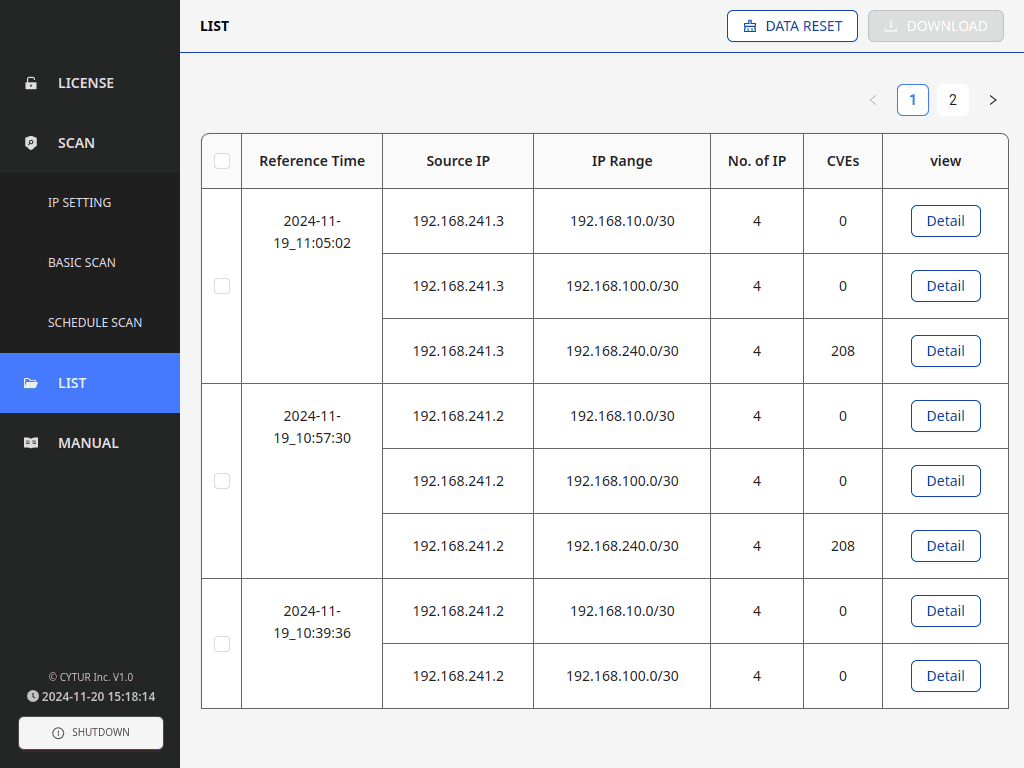
Equipment History Management & Integrated Control
Change History Tracking
Manages all scan results and equipment data in an integrated list format. Tracks inspection history to verify at a glance when equipment was added and how it changed, proving inventory consistency throughout the entire process from construction to delivery.
Data-Driven Security Vulnerability Diagnosis
Vulnerability Analysis & Mitigation
Precisely inspects discovered equipment for security vulnerabilities and unnecessary connections. Cross-references the latest security databases to pinpoint risks, provides specific mitigation recommendations for identified weaknesses, and serves as objective technical evidence for class certification.
Use Cases
Application Scenarios
🔍
Pre-Delivery Equipment Verification: Security Integrity Before Installation
Scenario
Before physically installing equipment on vessels, shipyards or suppliers connect CYTUR-SC® during the configuration stage to pre-scan assets
Proactive Response
Identifies potential vulnerabilities within devices in advance, verifying that security configurations are completed according to design before installation
Expected Outcome
Prevents equipment with security defects from being installed on vessels, reducing post-installation remediation costs
👻
Asset Management Automation: Shadow Device Discovery
Scenario
Activates automated scanning in complex vessel network environments with thousands of intertwined IT/OT devices
Proactive Response
Automatically discovers and classifies unidentified shadow assets connected to the network without authorization but missing from the inventory
Expected Outcome
Achieves complete control and visibility over all onboard equipment that is impractical to verify manually
🔧
Security Remediation: Vulnerability Resolution & Compliance Check
Scenario
Performs detailed inspections of security weaknesses (open ports, outdated software, etc.) found in identified assets
Proactive Response
After implementing system-recommended mitigations, performs re-scans to confirm threats have been completely eliminated
Expected Outcome
Ensures stability by delivering systems or transitioning to operations only after security has been verified
🚢
Final Pre-Delivery Verification: Proving Security Reliability for Ship Owners
Scenario
After construction completion, performs final full network scans with portable CYTUR-SC® during sea trials or immediately before delivery
Proactive Response
Conducts comprehensive surveys of network configurations that may have changed during installation and newly added equipment security status
Expected Outcome
Provides confidence through objective scan data that the vessel is 'cyber-security verified and safe', supporting smooth and secure operations
Certifications
International Class Certifications

Innovation Endorsement
for Product & Solution 2025

NovelTech.Approval
Marine Cyber Security
Start Objective Verification of Vessel Security
Want to learn more about CYTUR-SC®? Request a consultation today.