DESIGN PHASE
CYTUR-TM®
Threat Modeler
Maritime Cyber Threat Analysis Solution
An intelligent threat modeling solution that generates virtual network maps from vessel design data, simulates potential attack paths in advance, and helps establish optimal defense strategies.
Why You Need It
Why Cybersecurity Must Start at the Design Phase
🔧
Eliminate Security Flaws at the Design Stage
Discovering security issues after construction leads to massive additional costs and extended timelines. Predicting and addressing security risks from the design stage is the most rational approach.
🌐
Increasingly Complex Vessel Networks
With the adoption of smart ship technologies, interconnections between navigation, engine, and control systems have grown increasingly complex — requiring a system-wide approach to incident prevention beyond individual equipment security.
📋
Mandatory IACS UR E26/E27 Compliance
Since July 2024, IACS regulations require all new builds to identify system vulnerabilities from the design stage and demonstrate the adequacy of their Incident Response Plans (IRP).
Key Benefits
The Value CYTUR-TM® Delivers
01
Cost Reduction
Minimize Post-Construction Risks Through Design-Stage Flaw Elimination
Proactive security flaw prevention
Eliminate or significantly reduce the massive redesign and equipment replacement costs that arise when security vulnerabilities are discovered after construction or delivery.
Avoid unnecessary rework
By identifying security threats during the design phase, minimize the risk of workforce deployment and resource waste caused by last-minute design changes before delivery.
Eliminate or significantly reduce the massive redesign and equipment replacement costs that arise when security vulnerabilities are discovered after construction or delivery.
Avoid unnecessary rework
By identifying security threats during the design phase, minimize the risk of workforce deployment and resource waste caused by last-minute design changes before delivery.
02
On-Time Delivery
Streamline Class Certification and Shorten Review Periods
Efficient risk assessment
Automate the risk assessment process that previously took weeks of manual work, generating objective, data-driven reports rapidly.
Full regulatory compliance
Provide reports that comply with the latest international standards such as IACS UR E26/E27, dramatically reducing class society review preparation time.
Automate the risk assessment process that previously took weeks of manual work, generating objective, data-driven reports rapidly.
Full regulatory compliance
Provide reports that comply with the latest international standards such as IACS UR E26/E27, dramatically reducing class society review preparation time.
03
Operational Safety
Strengthen Fleet-Wide Incident Response Through Visualized Security Controls
Intuitive threat management
Visualize complex vessel networks by zone, enabling managers without specialized security expertise to monitor and control overall system risk at a glance.
Block incident propagation paths
Through virtual attack scenario simulations, identify and preemptively block the paths through which threats can spread from compromised equipment to critical zones such as the engine room or bridge, ensuring fleet-wide cyber survivability.
Visualize complex vessel networks by zone, enabling managers without specialized security expertise to monitor and control overall system risk at a glance.
Block incident propagation paths
Through virtual attack scenario simulations, identify and preemptively block the paths through which threats can spread from compromised equipment to critical zones such as the engine room or bridge, ensuring fleet-wide cyber survivability.
Key Features
Core Capabilities
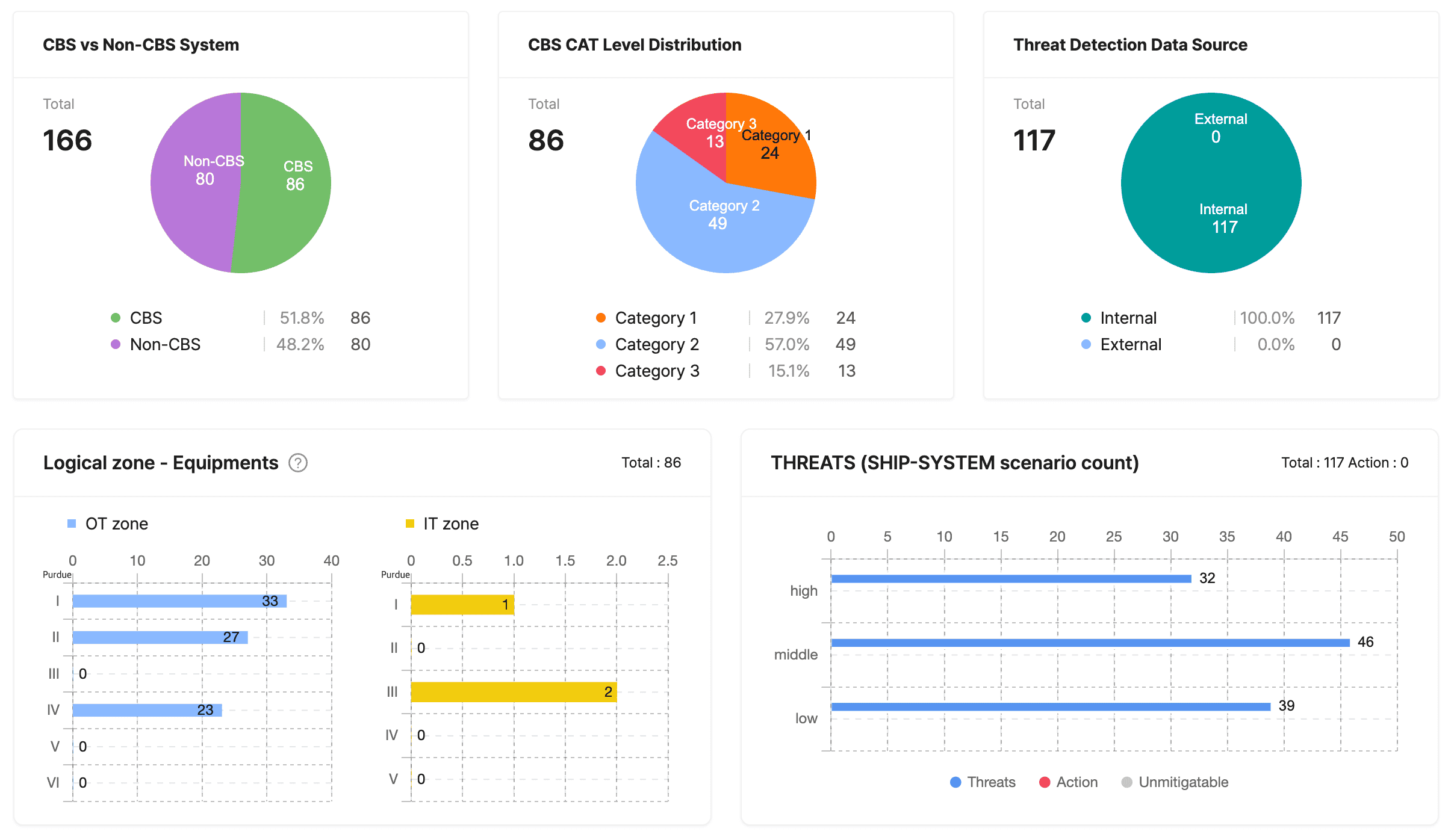
Intelligent Network Auto-Analysis
Maritime-Specific Security Blueprint Generation
Analyzes vessel design drawing data to map how each piece of equipment is connected, automatically generating a maritime-specific network topology. Visualizes the complex onboard control system architecture so managers can grasp the entire network at a glance.
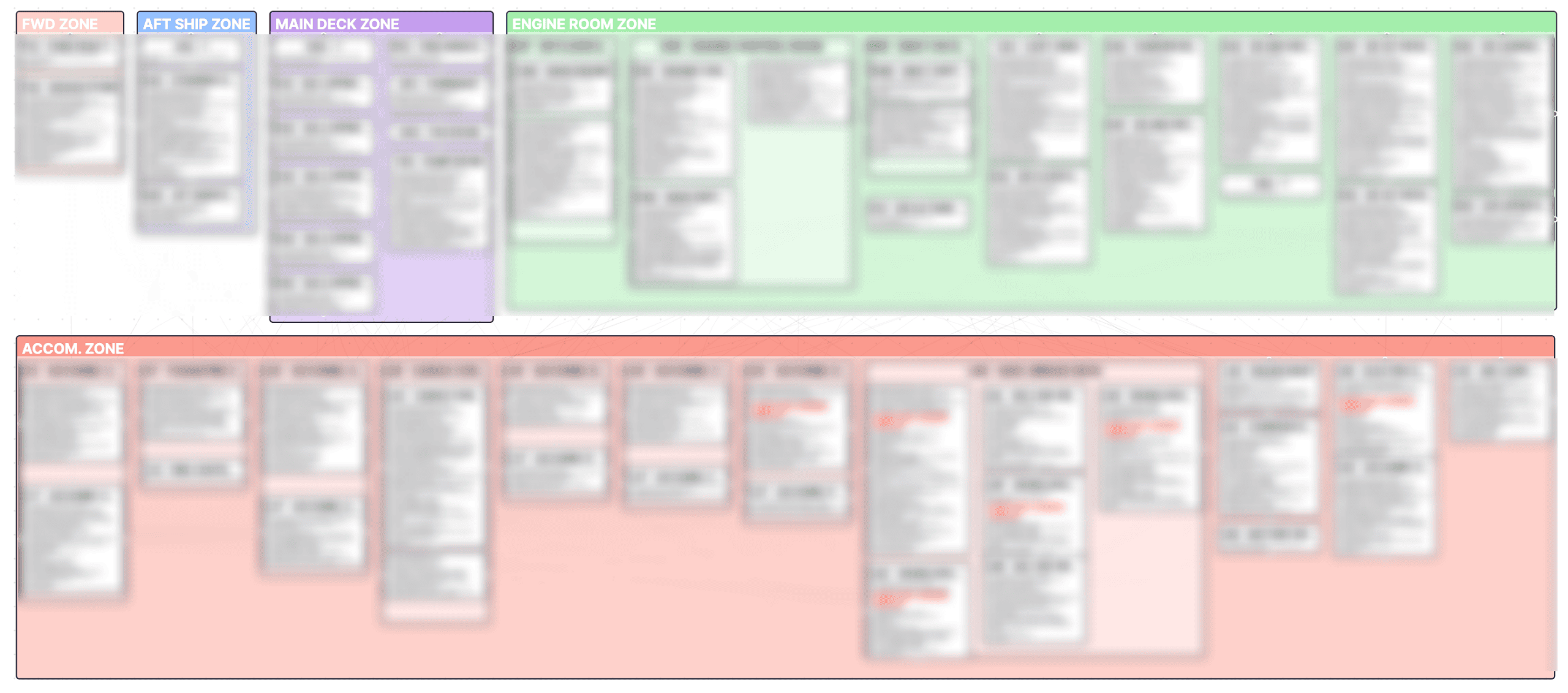
Zone-Based Security Analysis
Zone-Level Risk Management Canvas
Performs granular security analysis through workspaces designed around the vessel's physical spaces and logical zones. Accurately identifies hidden vulnerabilities and potential risks in each zone, and suggests practical countermeasures tailored to each zone's characteristics.
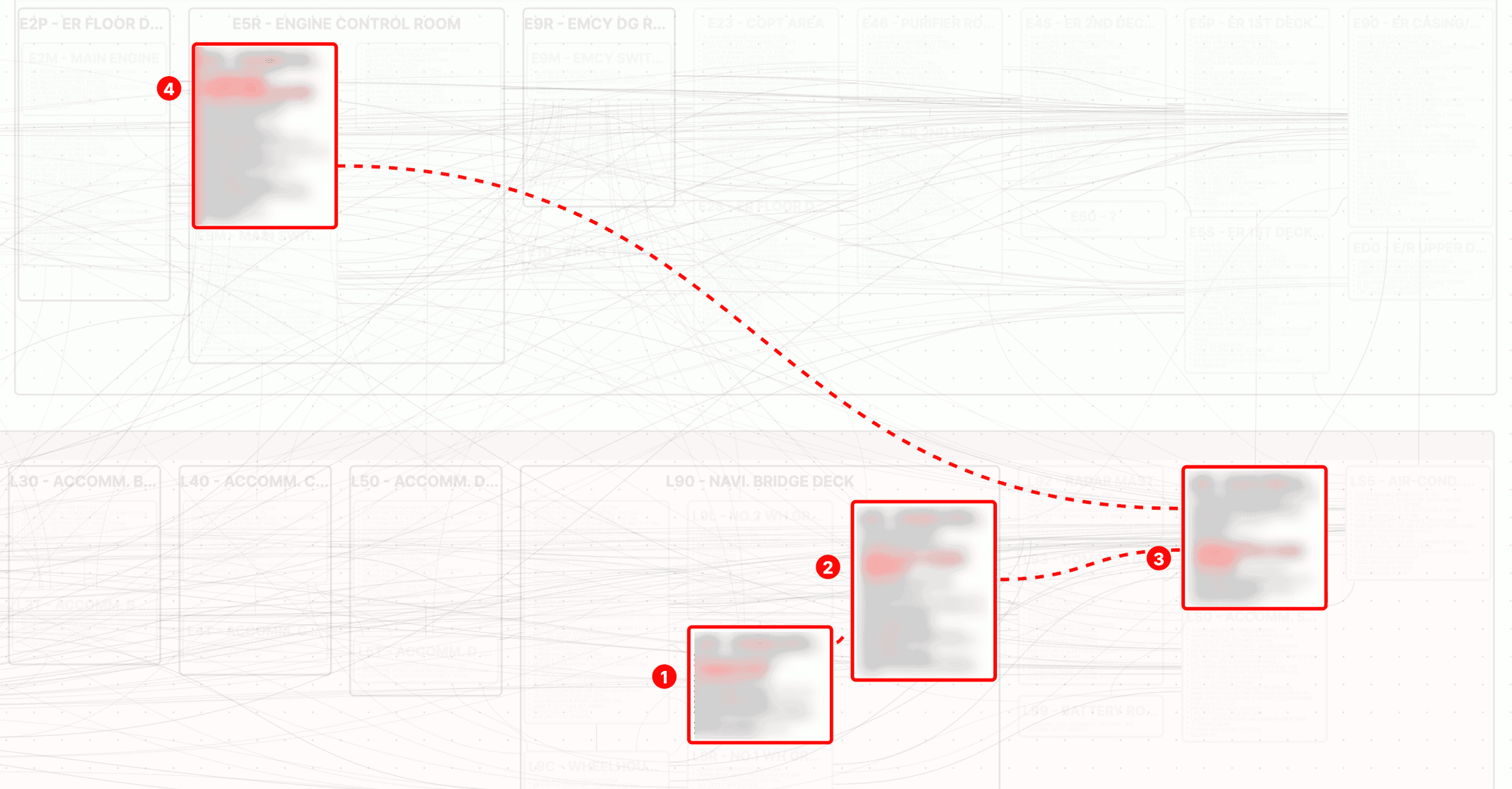
Virtual Attack Path Simulation
Incident Propagation Prediction & Blocking
Virtually recreates potential design-stage vulnerabilities to precisely analyze how threats could propagate through specific equipment weaknesses. Visually maps expected intrusion paths, providing powerful security insights to block entry points before an attack begins.
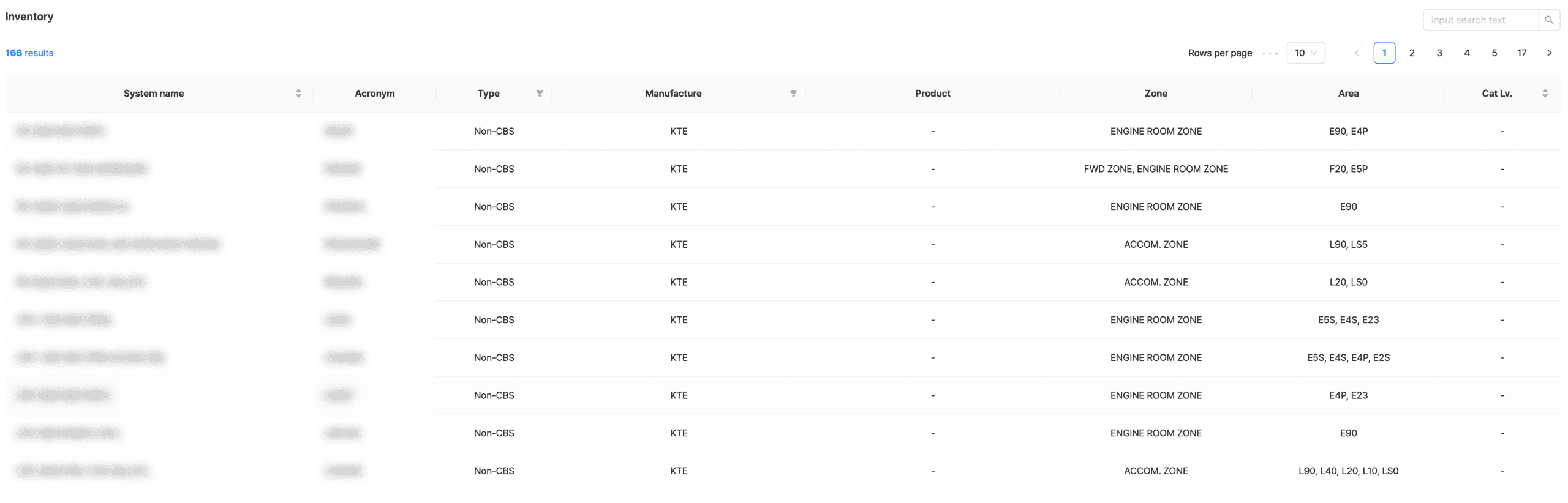
Integrated Asset Inventory Management
Equipment Security Database Construction
Automatically classifies extensive IT/OT equipment data by zone, providing a systematic consolidated inventory. Manages equipment location, type, and security classification in a database — eliminating security blind spots and meeting IACS UR E26/E27 asset management requirements.
Use Cases
Application Scenarios
🏗️
Shipyard Design Phase: Security by Design
Scenario
Automatically identify potential incident paths at system interconnection points based on early-stage design data such as network drawings
Proactive Response
Detect and eliminate security design flaws at the blueprint stage — flaws that would cost exponentially more to fix if found during or after construction
Expected Outcome
Minimize post-delivery management costs and risks, securing an economical and safe shipbuilding environment
📜
Class Certification: IACS UR E26/E27 Compliance
Scenario
Prepare the threat identification and risk assessment reports required for mandatory international cybersecurity regulation certification since 2024
Proactive Response
Automate the complex risk analysis process that previously took weeks of manual effort, establishing compliance strategies aligned with international standards
Expected Outcome
Prevent delivery delays due to non-compliance and dramatically shorten class society review preparation time
🛡️
Vulnerability Management: Zone-Level Incident Propagation Prediction
Scenario
Run virtual simulations to analyze how threats could spread to critical zones like the engine room or bridge when specific equipment is compromised
Proactive Response
Use the analysis canvas to identify zone-level vulnerabilities and visually analyze propagation paths to determine optimal firewall placement and network segmentation points
Expected Outcome
Prevent redundant security equipment investment while efficiently protecting critical zones
📦
Asset Optimization: Equipment Inventory-Based Management
Scenario
Automatically classify thousands of IT/OT equipment entries installed onboard by zone and build a consolidated management database
Proactive Response
Set criticality and security grades for each asset, establishing a system to track all equipment confirmed from the design stage at a glance
Expected Outcome
Complete the management foundation that enables impact assessment for any equipment defect discovered during future maintenance
Certifications
International Class Certifications

Innovation Endorsement
for Product & Solution 2025

Novel Tech. Approval
Certified Technology
Cyber Resilience That Starts at the Design Stage
Want to learn more about CYTUR-TM®? Request a consultation today.