CYBERSECURITY BY DESIGN
CYTUR-SHIPPOT
Ship Honeypot
Maritime Cyber Deception Solution
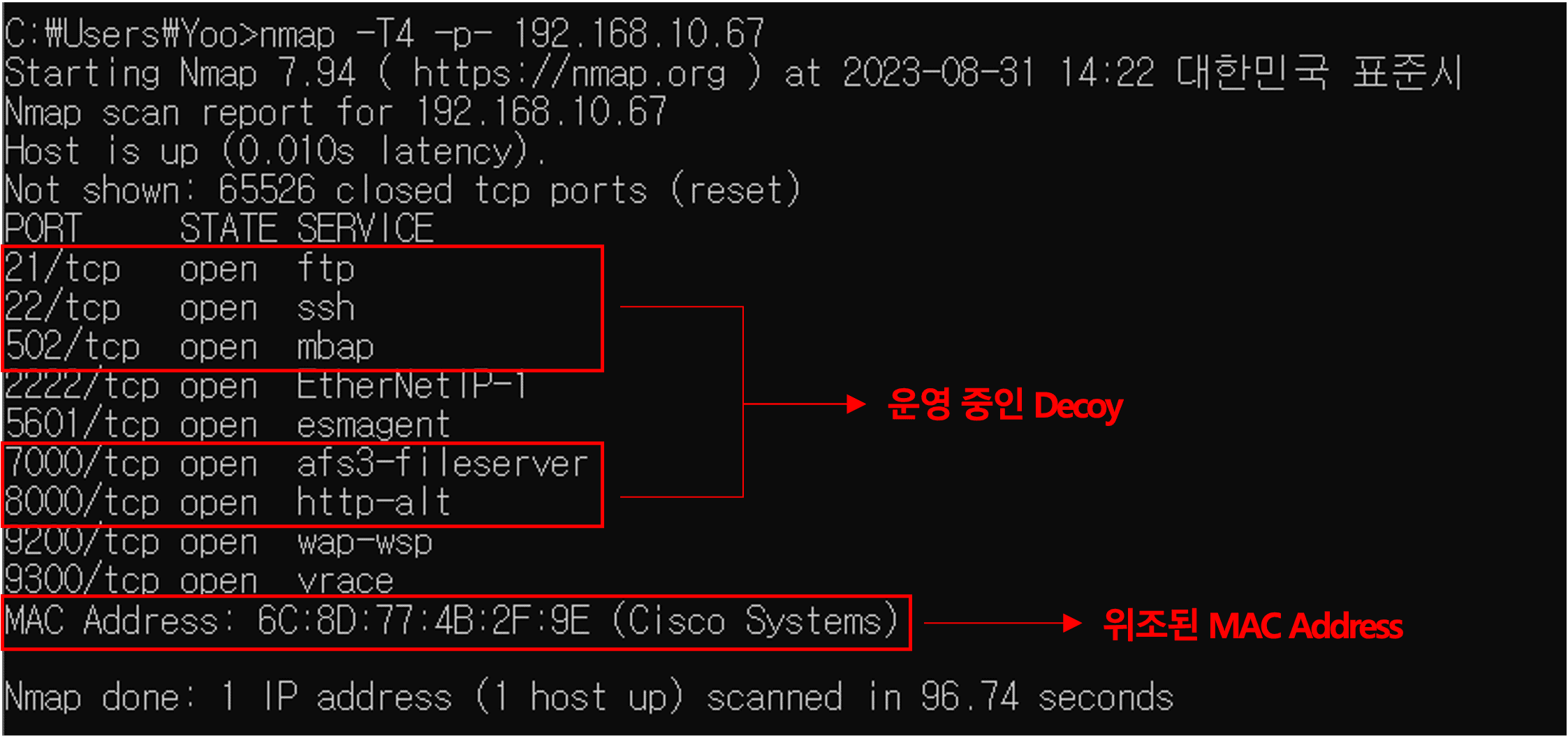
A maritime-specific cyber deception solution that deploys fake ship systems (Decoys) to lure attackers, enabling early attack detection and intent analysis to protect real assets. Based on the concept of 'phishing the hacker,' it redirects attackers to decoy systems before they reach actual control systems (CBS), analyzing attack techniques and patterns while keeping real assets safe through an offensive defense framework.
Key Features
Core Capabilities
Maritime-Specific Decoy
Ship System Emulation
Goes beyond generic IT servers to create fake systems that precisely emulate real ship management system login screens and maritime network communication (NMEA) protocols, perfectly deceiving attackers.

Kill Chain-Based Threat Detection
Full Attack Lifecycle Monitoring
Monitors the entire attack process (Reconnaissance → Weaponization → Delivery). Detects threats at each stage, from initial reconnaissance activities like port scanning to brute force attacks and abnormal web/SSH access attempts.

Real-Time Attack Dashboard
Comprehensive Threat Visibility
Integrates Snort-based detection engine with ELK stack (Elasticsearch, Kibana) to provide real-time visualization of intrusion counts, attacker IPs, targeted protocols (HTTP, FTP, Modbus, etc.), and attack frequency through an intuitive dashboard.

Secondary Attack Blocking & Security Integration
Automated Threat Response
Automatically shares attacker IPs and malicious behavior information captured by decoy systems with existing security equipment such as firewalls and IPS, instantly blocking secondary attacks targeting real systems.
Key Benefits
Expected Benefits of CYTUR-SHIPPOT
01
Early Detection
Early Identification of Attack Indicators & Containment
Detects hacker approaches from the reconnaissance stage before critical systems are compromised. This secures the golden time window and integrates with other security equipment to fundamentally prevent damage from spreading.
02
Threat Intelligence
Maritime-Specific Threat Intelligence Acquisition
Goes beyond simple blocking to collect and analyze specific attack logs — which ID/PW combinations attackers attempt, which protocols (SSH, FTP, Modbus) they target — enabling identification of attack patterns specifically targeting your vessels.
03
Operational Safety
Guaranteed Operational System Safety
All deception modules operate in a secure environment logically isolated from the actual operational network. Even if an attacker compromises the decoy system, there is absolutely no impact on the real vessel navigation systems.
Use Cases
Use Case Scenarios
🔍
[External Intrusion] Detecting Hacker Reconnaissance Against Ship Systems
Scenario
Hackers may attempt scanning from outside the vessel via satellite communications to find vulnerable equipment (IP/Port) on the internal network.
Application
SHIPPOT exposes fake vulnerabilities more attractive than real equipment to instantly detect scanning activity, blocking attacker IPs at the reconnaissance stage before any attack code is deployed, neutralizing the intrusion itself.
👤
[Insider Threat] Identifying Unauthorized Access by Crew & Maintenance Vendors
Scenario
Crew members or maintenance vendor engineers may attempt to access critical control systems (AMS, etc.) without authorization, whether out of curiosity or malicious intent.
Application
When anyone attempts to log in (ID/PW input) to a Decoy disguised as a critical system, an immediate alert is triggered. Monitors lateral movement within the internal network and detects unauthorized system access attempts.
🦠
[Ransomware] Preventing Automated Bot & Malware Propagation
Scenario
A single onboard PC becomes infected with ransomware and is automatically searching for other propagation targets within the network.
Application
SHIPPOT opens multiple virtual IPs and services (SMB, FTP, etc.) to lure ransomware, allowing fake systems to absorb the attack instead of real critical data servers, slowing propagation speed and enabling early detection of the infection.
🛡️
[Defense/Security] Meeting Cyber Survivability Requirements for Special Vessels
Scenario
When building modern destroyers or special-purpose vessels, military specifications or security regulations requiring disruption of enemy cyber attacks must be met.
Application
Deploy SHIPPOT to install virtual booby traps across the vessel network, establishing a deception defense framework that meets naval and special vessel security requirements and induces confusion in enemy cyber attacks during wartime scenarios to enhance survivability.
Protect Your Vessels with Proactive Cyber Defense
To learn more about CYTUR-SHIPPOT, request a consultation today.