OPERATE
CYTUR-MG
Maritime Guard
Intelligent Integrated Cyber Resilience Platform for Vessels
Network monitoring (NS), threat analysis (TA), and risk management (RM) capabilities
unified into a single platform, enabling thorough vessel security management without specialized experts — an intelligent integrated cyber resilience platform.
Why You Need It
Why an Integrated Management Platform Is Essential
📋
Sustainable Certification Maintenance Required
Under IACS UR E26 regulations mandatory since July 2024, vessels must maintain up-to-date asset inventories and network diagrams for annual submission to classification societies even after delivery.
📄
Limitations of Document-Based Management
Manual or spreadsheet-based approaches are prone to discrepancies with actual vessel data and have poor collection efficiency. Failure to reflect equipment replacements or software updates in real time during operations can lead to errors in annual inspections or increased security incident risks.
🔄
Automated Real-Time Management Needed
Only a system that tracks complex vessel network changes in real time and automatically monitors and manages security threats can comply with strengthened international regulations and ensure fleet safety.
Platform Overview
Intelligent Cyber Integrated Control Center for Vessels
Consolidates and analyzes threat data from all onboard equipment, automatically handling complex international regulatory compliance tasks.
| Category | COLLECT (Data Collection) | ANALYZE (Data Analysis) | MANAGE (Data Management) |
|---|---|---|---|
| Core Role | Collect internal/external vessel risk information | Analyze risk relationships across equipment | Manage security threats and generate reports |
| Key Functions | Collect and integrate vessel-targeted threat data | Aggregate scattered equipment data to identify threat connections | Conduct risk assessments and auto-generate class submission reports |
| Components | NS (Network Sensor) SD (Ship Defender) TI (Threat Intelligence) SHIPPOT (Ship Honeypot) | TA (Threat Analyzer) | RM (Risk Manager) |
COLLECT (Data Collection)
Core RoleCollect internal/external vessel risk information
Key FunctionsThreat data collection & integration
ComponentsNS · SD · TI · SHIPPOT
ANALYZE (Data Analysis)
Core RoleAnalyze inter-equipment risk relationships
Key FunctionsIdentify threat connections
ComponentsTA (Threat Analyzer)
MANAGE (Data Management)
Core RoleManage security threats and generate reports
Key FunctionsAuto-generate class submission reports
ComponentsRM (Risk Manager)
Key Benefits
The Value CYTUR-MG Delivers
01
Operational Safety
Strengthen Vessel Operational Safety and Preemptively Block Incident Risks
Maritime-specific threat detection
Identifies GPS spoofing attacks that conventional security equipment cannot detect, ensuring navigation system reliability.
Real-time unauthorized device monitoring
Instantly detects unauthorized assets connected during maintenance or devices not in design blueprints, closing security gaps.
Economic loss prevention
Prevents vessel shutdown incidents caused by cyber attacks, enhancing fleet cyber survivability and reducing massive repair costs.
Identifies GPS spoofing attacks that conventional security equipment cannot detect, ensuring navigation system reliability.
Real-time unauthorized device monitoring
Instantly detects unauthorized assets connected during maintenance or devices not in design blueprints, closing security gaps.
Economic loss prevention
Prevents vessel shutdown incidents caused by cyber attacks, enhancing fleet cyber survivability and reducing massive repair costs.
02
Compliance
Automate Compliance Response and Reduce Administrative Costs
Automated certification documents
The system automatically generates up-to-date asset inventories, network diagrams, and risk management records required for annual class inspections.
Maximize operational efficiency
Automates extensive documentation tasks previously done manually, dramatically reducing administrative time for personnel.
Eliminate certification delay risks
Removes certification errors and delay risks caused by human error, ensuring vessels are delivered and operated on schedule.
The system automatically generates up-to-date asset inventories, network diagrams, and risk management records required for annual class inspections.
Maximize operational efficiency
Automates extensive documentation tasks previously done manually, dramatically reducing administrative time for personnel.
Eliminate certification delay risks
Removes certification errors and delay risks caused by human error, ensuring vessels are delivered and operated on schedule.
03
Integrated Control
Achieve Multi-Dimensional Integrated Control Through CYTUR Solution Integration
Security data consolidation
Consolidates data from all individually operating CYTUR solutions including ASA, TI, TM, SD, and SHIPPOT into a single screen (TA).
Deep correlation analysis
Connects and analyzes previously scattered threat information, achieving multi-dimensional security visibility across the entire vessel.
Intelligent attack response
Accurately identifies the context of sophisticated hacking attacks, providing the fastest and most precise response guidance when incidents occur.
Consolidates data from all individually operating CYTUR solutions including ASA, TI, TM, SD, and SHIPPOT into a single screen (TA).
Deep correlation analysis
Connects and analyzes previously scattered threat information, achieving multi-dimensional security visibility across the entire vessel.
Intelligent attack response
Accurately identifies the context of sophisticated hacking attacks, providing the fastest and most precise response guidance when incidents occur.
Key Features
Core Capabilities
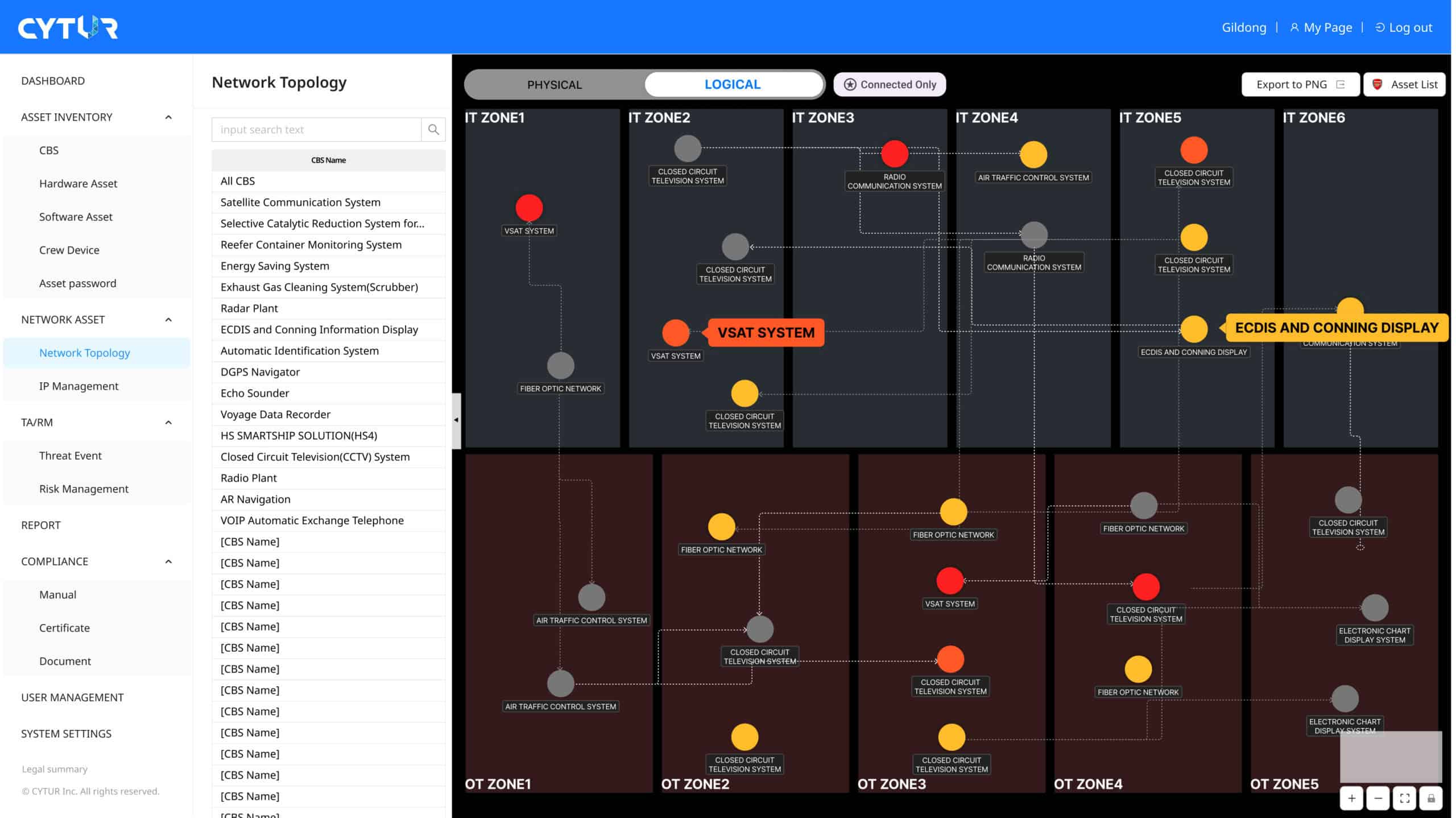
Real-Time Asset Inventory & Network Diagram Auto-Update
Digital Management Ledger Automation
Collects data from onboard network equipment to monitor all Computer-Based Systems (CBS) in real time. Instantly detects equipment additions or changes, reflects them in the asset inventory, and automatically generates up-to-date network topology diagrams to maintain continuous regulatory compliance.
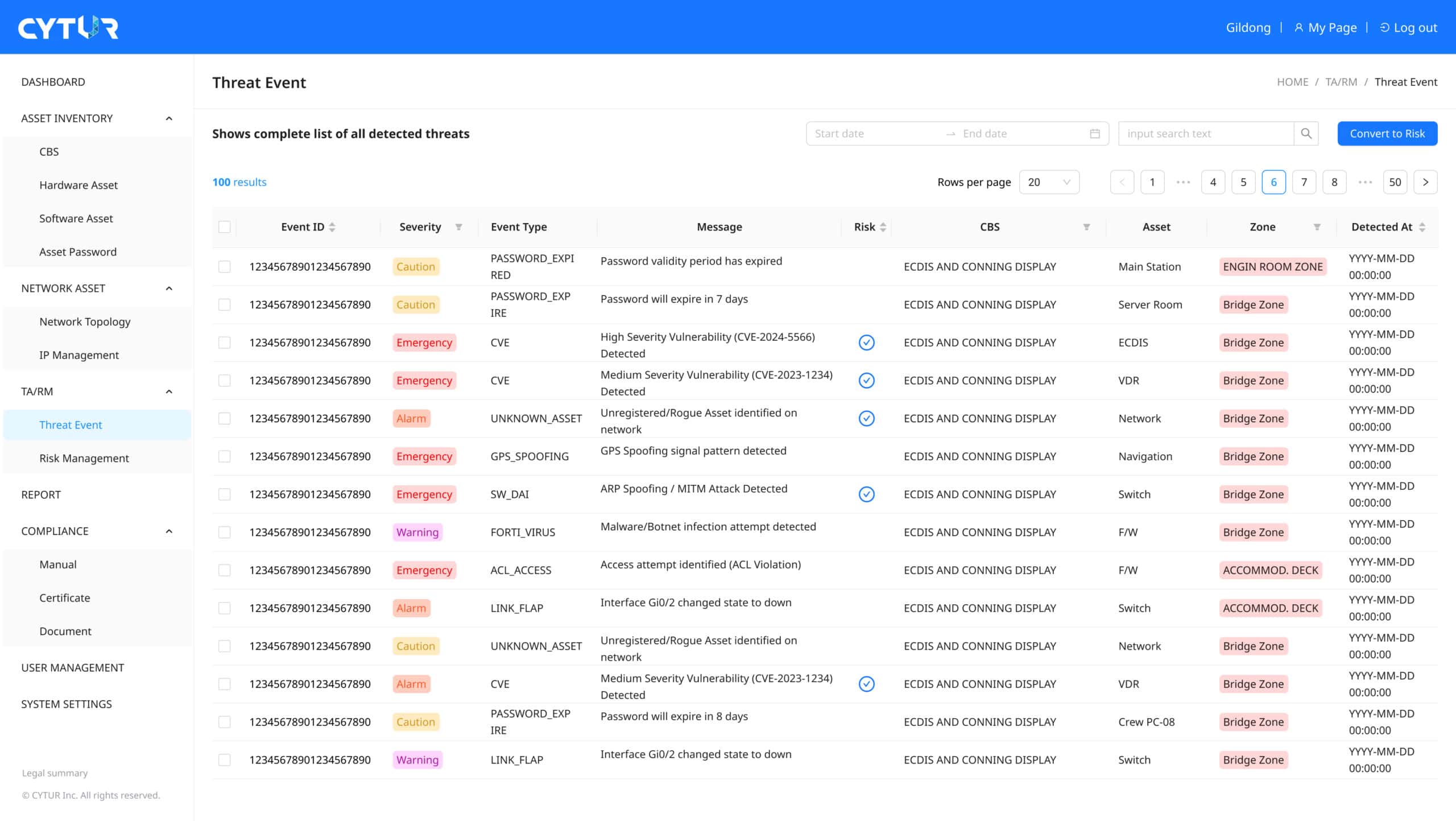
Intelligent Anomaly Detection & Risk Analysis
AI-Powered Security
Analyzes data flowing through the network to capture abnormal access or suspicious activity. Filters only genuinely dangerous items and visualizes them by risk level, combining latest vulnerability intelligence to identify potential weaknesses before hackers do.
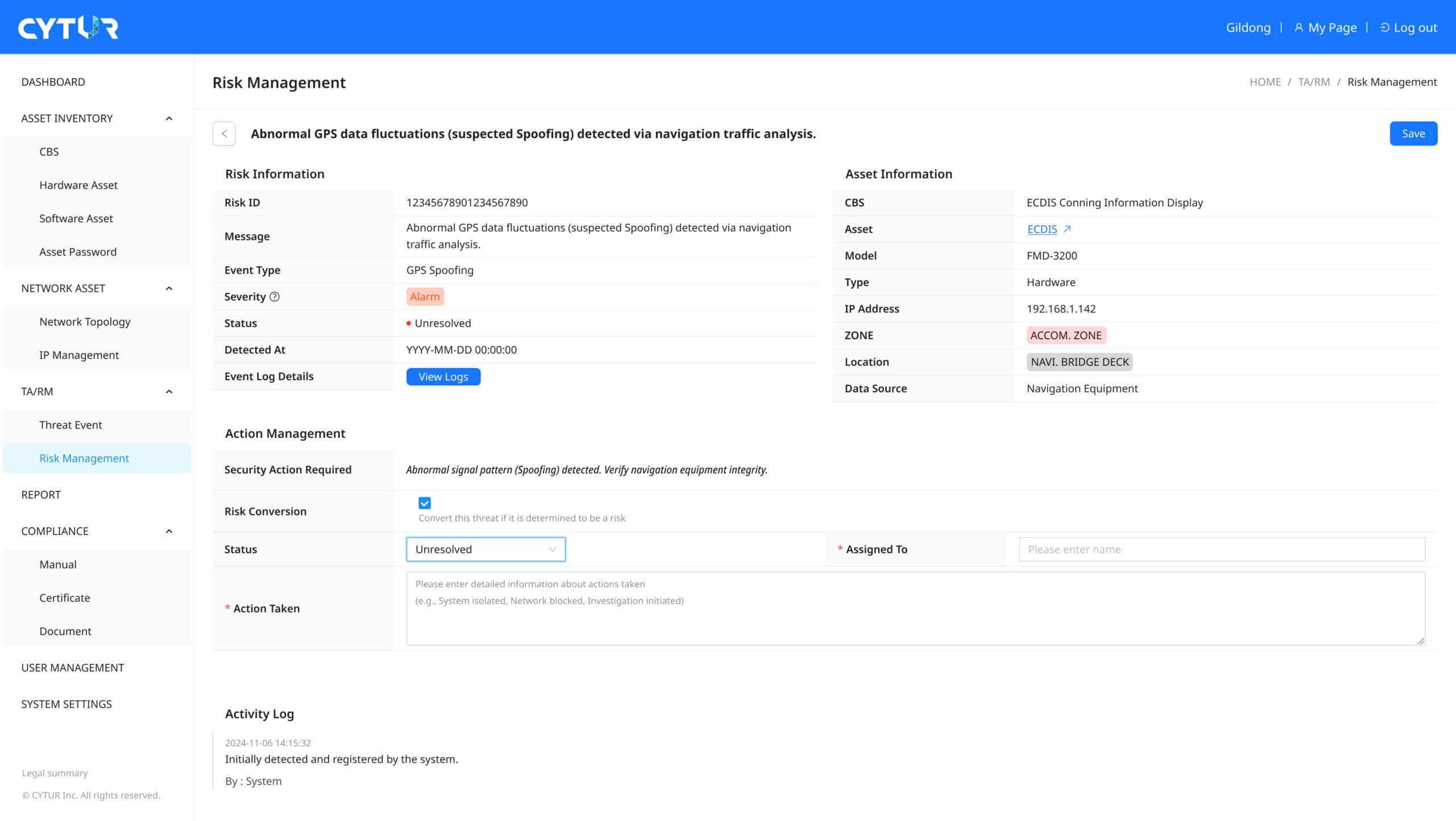
Maritime Communication Analysis & GPS Spoofing Detection
Navigation Safety Assurance
Directly collects and analyzes specialized communication data (NMEA) used by navigation equipment (ECDIS, etc.). Detects GPS spoofing attacks — a major maritime security threat — in real time, ensuring autonomous and smart vessels stay on their planned routes.

Class Certification Management & Risk Action History Reporting
Compliance Hub
Automatically generates risk management records required for annual class submission to maintain IACS UR E26/E27 certification. Records every step from the moment a risk is discovered through how personnel responded and the outcome, serving as critical evidence to reduce legal liability in future incidents.
Use Cases
Application Scenarios
📜
Class Annual Survey: Automated Documentation & Evidence
Scenario
Annual class surveys require up-to-date asset inventories and network diagrams, but manual update omissions cause discrepancies between actual status and documentation
Proactive Response
Instantly outputs IACS UR E26-optimized reports based on automatically collected asset change histories and real-time network configurations
Expected Outcome
Dramatically reduces administrative costs by providing up-to-date evidence required by class societies without dedicated audit personnel
👻
Shadow Asset Detection: Real-Time Unauthorized Device Management
Scenario
When unidentified assets (PLCs, servers, etc.) temporarily connected by maintenance engineers or installed without being documented create security blind spots
Proactive Response
Network Sensor (NS) analyzes data in real time to instantly detect unregistered connections not in the inventory and alerts administrators
Expected Outcome
Verify device location through the dashboard and immediately decide whether to disconnect, completely blocking security vulnerabilities
📡
Navigation Safety: GPS Spoofing Attack Prevention
Scenario
When there is concern about attacks injecting false GPS signals targeting autonomous and smart vessels to divert them from routes or cause collisions
Proactive Response
Directly analyzes onboard network communication data (NMEA) to precisely verify the integrity of position information values
Expected Outcome
Immediately triggers alarms when abnormal position manipulation patterns are detected, enabling operators to switch to manual navigation or prevent incidents
📂
Risk Management Compliance: Action Documentation & History Tracking
Scenario
When filtering actionable risks from numerous security alerts and facing class criticism for lack of documented response processes
Proactive Response
Designates critical items among detected threats as 'Risks' and records every step within the system from personnel assignment through action completion
Expected Outcome
Accumulated history serves not only as evidence for class certification maintenance but also as documentation to reduce legal liability in security incidents
Architecture
CYTUR-MG Architecture
COLLECT
NS
Network Sensor
Analyzes vessel network traffic to automatically identify all connected CBS assets and detect shadow assets in real time.
COLLECT
SD
Ship Defender
Uses AI to analyze maritime-specific communication protocols (NMEA, Modbus, etc.) to detect abnormal access or data manipulation.
COLLECT
TI
Threat Intelligence
Monitors the dark web and external sources in real time to identify the latest hacking techniques targeting the maritime industry and detect data leaks.
COLLECT
SHIPPOT
Ship Honeypot
Deploys decoy equipment disguised as real vessel systems to lure hackers, identify attack intentions, and contain damage propagation at the source.
ANALYZE
TA
Threat Analyzer
An intelligence center that consolidates data from all units into a single screen and analyzes correlations between threats.
MANAGE
RM
Risk Manager
Automatically generates asset inventories, network diagrams, risk management records and reports essential for IACS UR E26/E27 certification audits.
Packages
CYTUR-MG Packages
| Components | Standard | Advanced | Enterprise | |
|---|---|---|---|---|
| Collect | NS (Network Sensor) | ● | ● | ● |
| SD (Ship Defender) | ○ | ● | ● | |
| TI (Threat Intelligence) | ○ | ● | ● | |
| SHIPPOT (Ship Honeypot) | ○ | ○ | ● | |
| Analyze | TA (Threat Analyzer) | ● | ● | ● |
| Manage | RM (Risk Manager) | ● | ● | ● |
Standard
NS (Network Sensor)●
SD (Ship Defender)○
TI (Threat Intelligence)○
SHIPPOT (Ship Honeypot)○
TA (Threat Analyzer)●
RM (Risk Manager)●
Advanced
NS (Network Sensor)●
SD (Ship Defender)●
TI (Threat Intelligence)●
SHIPPOT (Ship Honeypot)○
TA (Threat Analyzer)●
RM (Risk Manager)●
Enterprise
NS (Network Sensor)●
SD (Ship Defender)●
TI (Threat Intelligence)●
SHIPPOT (Ship Honeypot)●
TA (Threat Analyzer)●
RM (Risk Manager)●
The Integrated Control Center for Maritime Cybersecurity
Want to learn more about CYTUR-MG? Request a consultation today.
