INTELLIGENCE
CYTUR-TI™
Threat Intelligence
Maritime Cybersecurity Threat Intelligence
A global vessel incident and equipment risk forecasting service that monitors cyber incident data and hacker dark web markets worldwide 24/7, analyzing in real time whether your fleet's equipment or internal data has been exposed to threats.
Why You Need It
Why Threat Intelligence Is Essential
🚨
Eliminating Cyber Incident Blind Spots
Conventional security approaches cannot tell you whether your vessel's engines, navigation (radar), and communication equipment are currently being targeted by hackers worldwide. Reactive responses after an incident has already occurred lead to massive operational downtime losses.
⚓
Lack of Maritime-Specific Intelligence
General IT security services used on land lack understanding of maritime-specific equipment and at-sea communication environments. A maritime-specialized threat forecasting system that truly understands your vessel's machinery and systems is essential.
📋
Tightening International Regulations
IACS UR E26 defines cyber resilience as a mandatory requirement for vessels and demands objective evidence that fleets are continuously analyzing the cyber threats they face for class certification purposes.
Key Benefits
The Value CYTUR-TI™ Delivers
01
Incident Prevention
Proactive Incident Blocking and Safe Operations
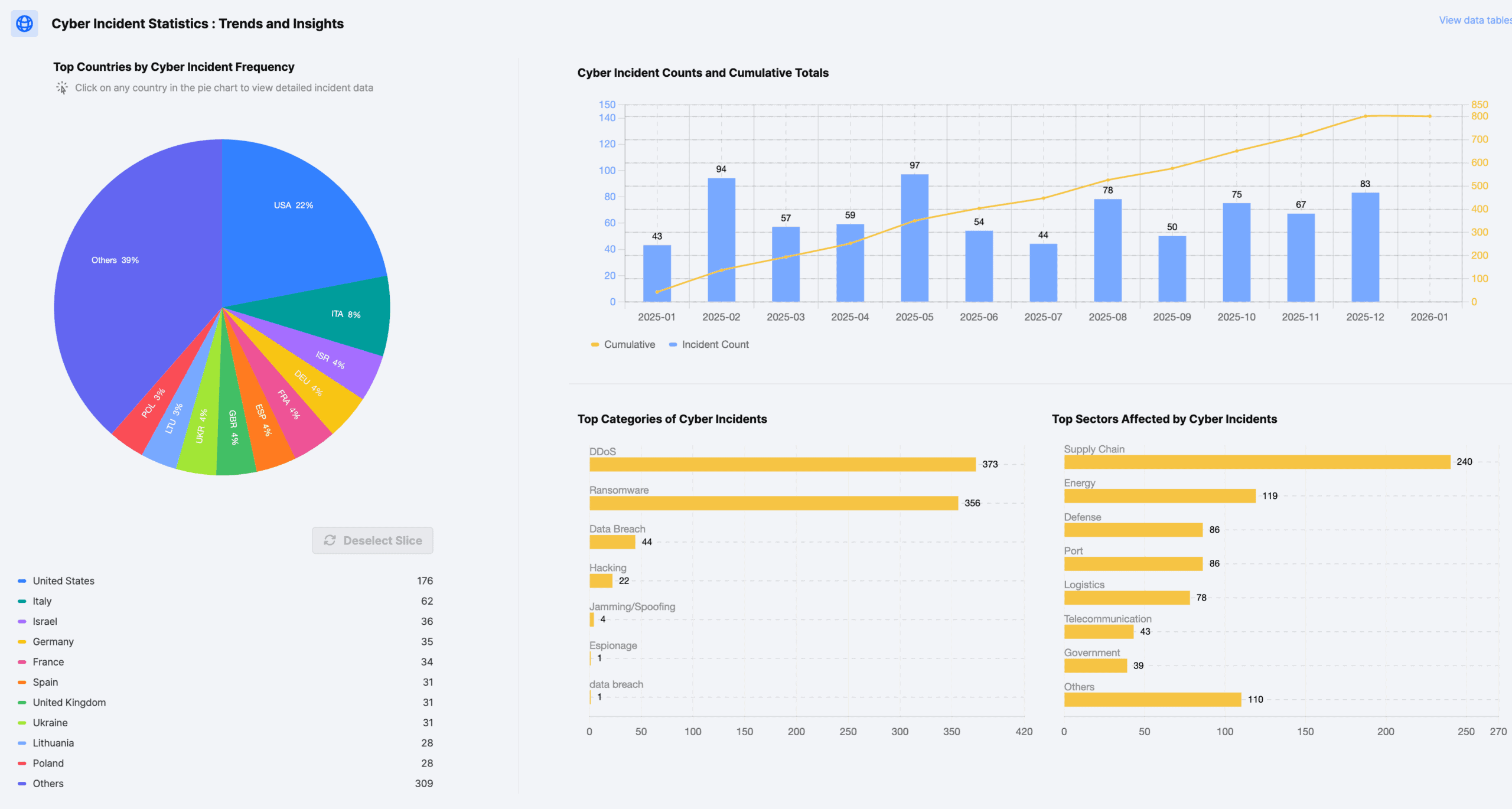
Real-world attack visualization
Visualizes actual hacking incidents worldwide (attack timing, methods, targeted equipment) on an interactive map.
Critical incident prevention
Take preemptive action before similar attacks reach your vessels, blocking catastrophic incidents such as engine shutdowns or course deviations at the source.
Visualizes actual hacking incidents worldwide (attack timing, methods, targeted equipment) on an interactive map.
Critical incident prevention
Take preemptive action before similar attacks reach your vessels, blocking catastrophic incidents such as engine shutdowns or course deviations at the source.
02
Cost Reduction
Reduce Operational Costs and Maximize Management Convenience
Remote security management
Without needing cybersecurity experts onboard each vessel, existing ship management personnel can monitor the security status of your entire fleet at a glance through cloud access.
Efficient maintenance planning
Build effective maintenance plans based on manufacturer-specific vulnerability information for each piece of equipment.
Without needing cybersecurity experts onboard each vessel, existing ship management personnel can monitor the security status of your entire fleet at a glance through cloud access.
Efficient maintenance planning
Build effective maintenance plans based on manufacturer-specific vulnerability information for each piece of equipment.
03
Certification Edge
Strengthen Global Credibility and Certification Competitiveness
Automated threat analysis reports
Automatically generates the threat analysis reports essential for maintaining class certifications such as IACS UR E26.
Enhanced business competitiveness
Shipyards can demonstrate they build "security-verified safe vessels," while ship owners can prove they operate "systematically managed fleets" to charterers worldwide.
Automatically generates the threat analysis reports essential for maintaining class certifications such as IACS UR E26.
Enhanced business competitiveness
Shipyards can demonstrate they build "security-verified safe vessels," while ship owners can prove they operate "systematically managed fleets" to charterers worldwide.
Key Features
Core Capabilities
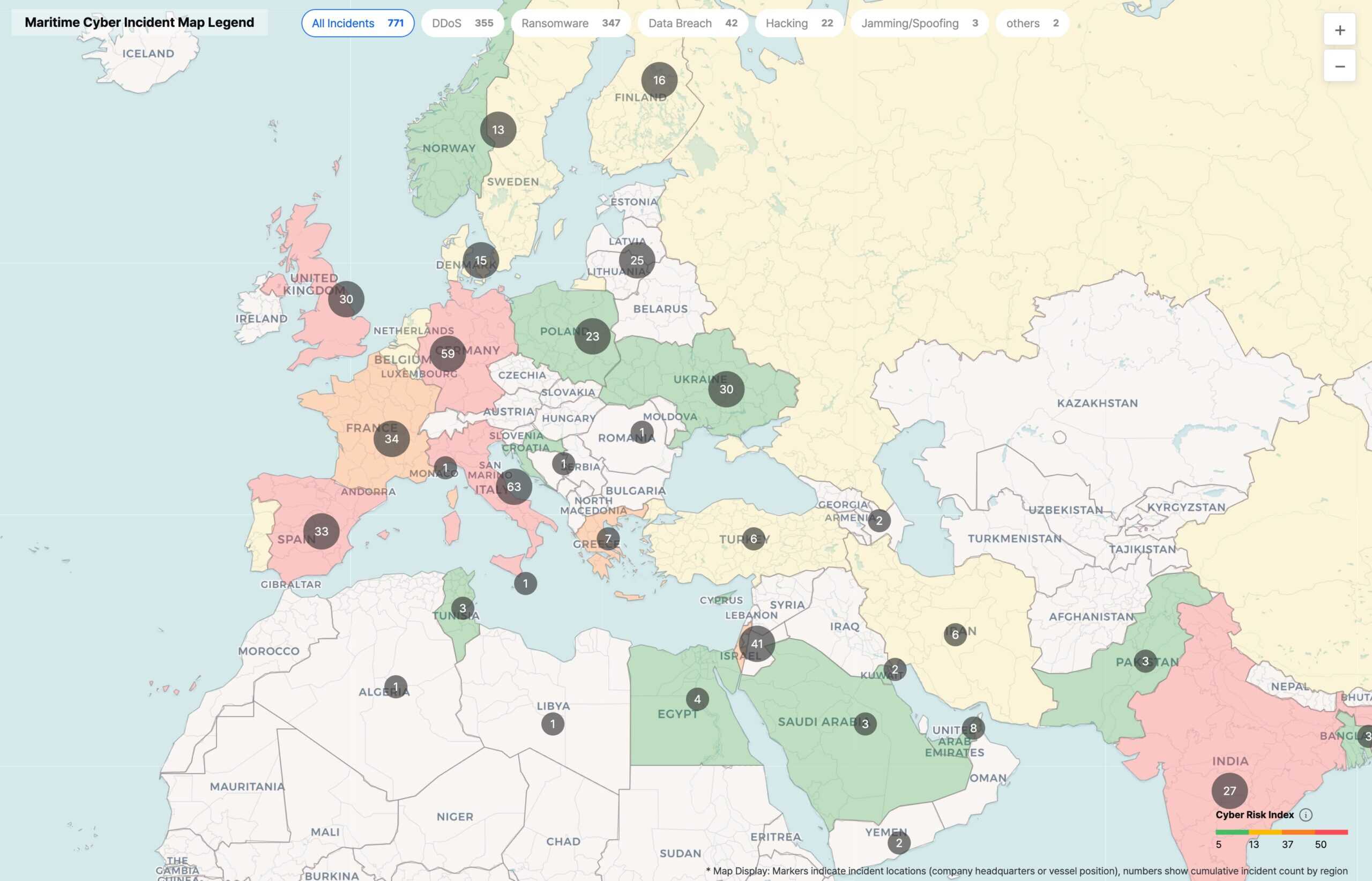
Real-Time Global Vessel Incident Radar
Threat Visibility
Collects cyber attack and incident data from seas worldwide in real time, visualizing them on an interactive map. Instantly identify what types of hacking incidents have occurred along your vessel's route or nearby waters, enabling preemptive defense before incidents spread to your fleet.
Onboard Equipment Vulnerability Diagnosis
Attack Surface Management
Analyzes security weaknesses and hacker intrusion paths for critical onboard systems (engine controls, navigation equipment, etc.). This is the process of finding "which doors on our ship are open." Identifies equipment-specific vulnerabilities in advance so they can be patched during maintenance before hackers exploit them.
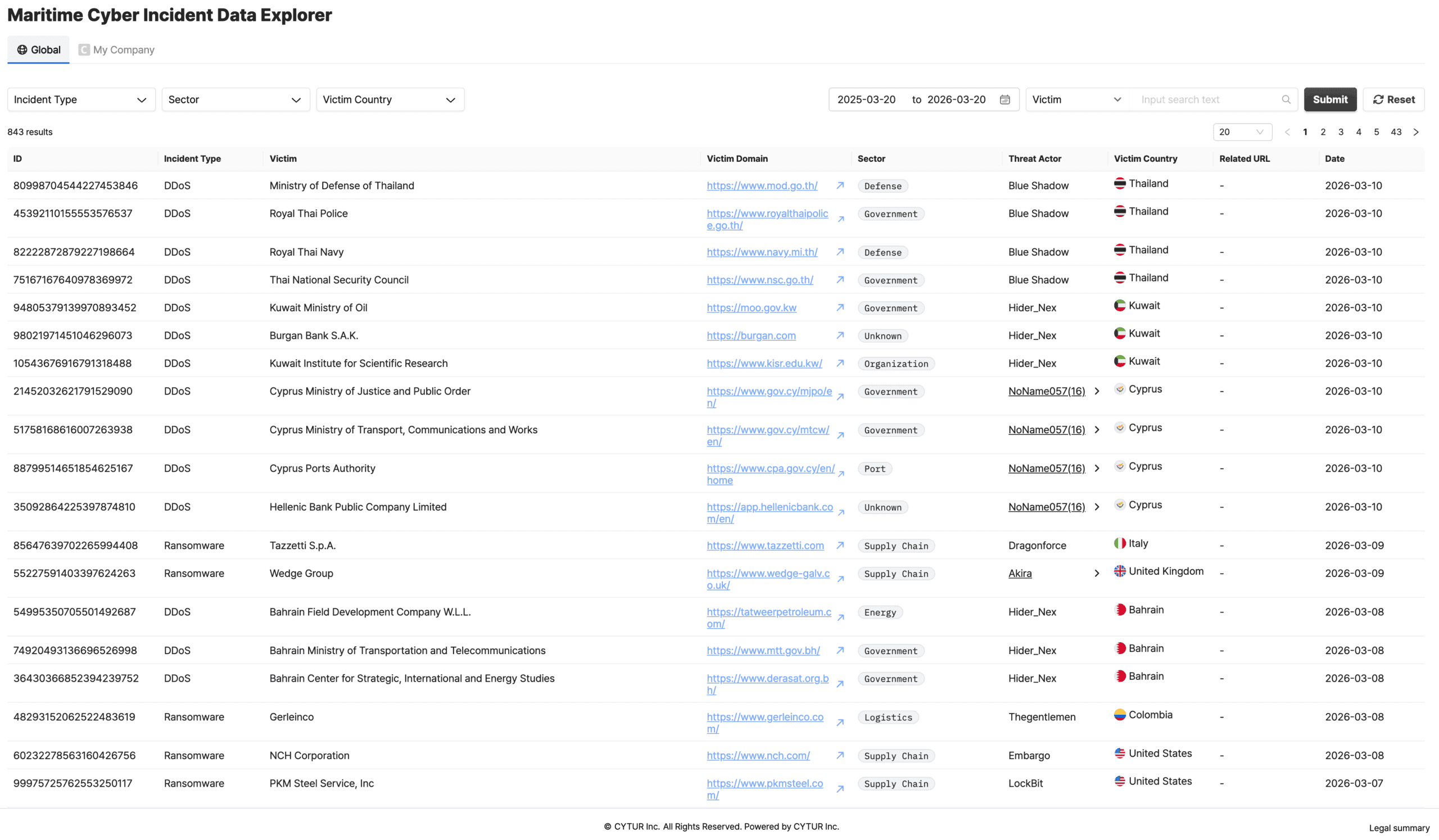
Unauthorized Data Leak Monitoring
Information Leak Surveillance
Monitors the dark web and underground hacker communities 24/7 to verify whether shipping company information has been leaked. Watches for unauthorized trading of critical assets such as admin credentials, passwords, or vessel design drawings, and guides immediate password changes and account lockdowns upon detection to prevent secondary damage.
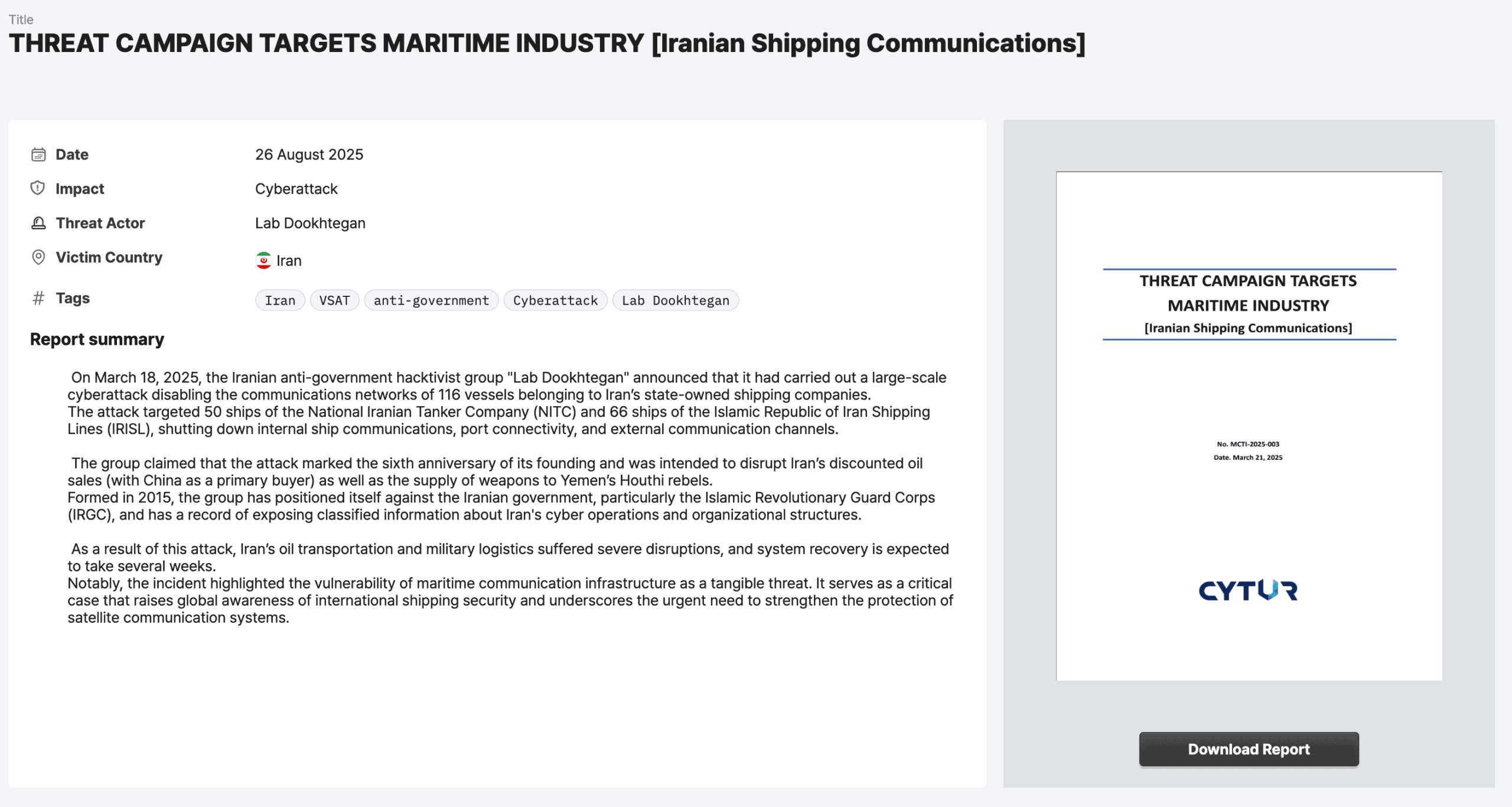
Intelligent Risk Forecast & Action Reports
Customized Intelligence
Publishes analytical reports tailored to each client's fleet composition, containing the latest hacking trends and specific action plans. These customized response reports can be used as security audit materials required by IACS international regulations.
Use Cases
Application Scenarios
🔐
Security Expert: Preemptive Blocking of Latest Attack Methods
Scenario
Analyze globally trending hacking techniques to proactively reinforce your vessel's systems
Proactive Response
Identify potential attack vectors against your organization based on the latest intelligence from dark web sources, and proactively update security policies before new techniques spread widely
Expected Outcome
Easily grasp the latest cyber threat trends to support practical security strategy development
🏢
Shipping Company Operations: Customized Risk Prevention
Scenario
Verify at the headquarters level whether admin accounts or critical data have been leaked externally and take immediate action
Proactive Response
Analyze company-specific information to instantly verify whether credentials have been exposed on the dark web, and leverage IACS-compliant analysis reports for regulatory and operational risk management
Expected Outcome
Respond immediately to threats and prevent incidents through customer-specific intelligence
🔧
Fleet Equipment Threat Assessment: Attack Surface Management
Scenario
Identify security weaknesses in specific onboard equipment in advance to preemptively close entry points for hackers
Proactive Response
Receive advance intelligence on which critical equipment (engines, ballast water systems, etc.) has security vulnerabilities, and complete security patches or network isolation before an actual attack occurs
Expected Outcome
Prevent vessel operational shutdowns caused by equipment vulnerabilities
🧭
Navigator & Operations Team: Security Hardening Before Entering Risk Zones
Scenario
Before entering dangerous waters or specific ports, review cyber incident information frequently reported in that region to establish heightened security posture
Proactive Response
Intuitively review global maritime cyber incident status via the real-time Cyber Accident MAP, and proactively elevate vessel security levels based on threat assessment of the planned route
Expected Outcome
Support safe navigation by providing real-time awareness of location-linked cyber threats
Certifications
International Class Certifications

Innovation Endorsement
for Product & Solution 2025
Protect Your Fleet with Real-Time Threat Intelligence
Want to learn more about CYTUR-TI™? Request a consultation today.
