Identify Threats
Before They Arrive
Cyber threats evolve faster than any individual vessel can track.
CYTUR monitors dark web, deep web, and global threat feeds 24/7,
proactively collecting and analyzing threats targeting the maritime industry.
Generic CTI Cannot Cover
Maritime-Specific Cyber Threats
General-purpose cyber threat intelligence (CTI) services used onshore
lack understanding of ship-specific equipment and maritime communication environments.
NMEA and AIS protocol vulnerabilities, leaked vessel access credentials,
and targeted attacks on maritime equipment manufacturers —
these maritime-specific threats cannot be covered by generic CTI.
— the key to proactive maritime defense
Threat Intelligence Solution
Threat Intelligence
Maritime-Specific Cyber Threat Intelligence Platform
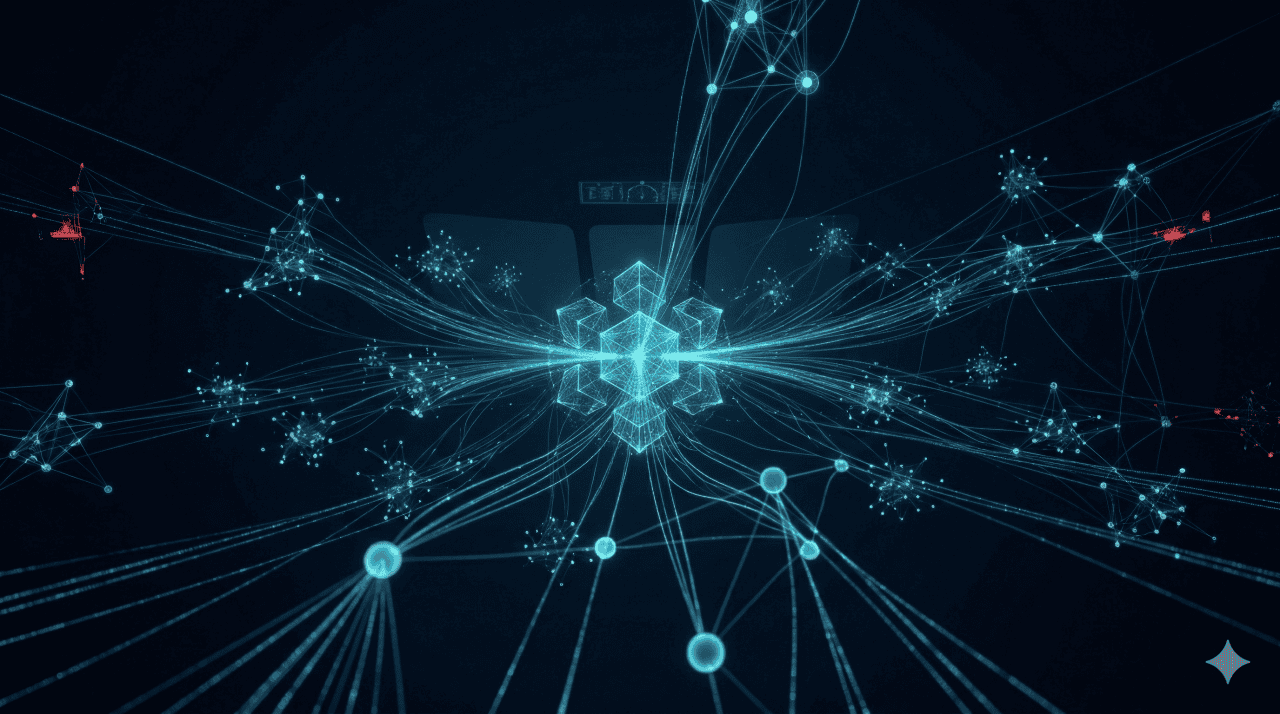
Real-time Global Maritime Incident Radar
Collects cyber attack and incident data from seas worldwide
in real-time and visualizes them on an interactive map.
24/7 Dark Web / Deep Web Monitoring
Continuously monitors hacker marketplaces (dark web) and encrypted channels
to detect leaks of shipping company-related information.
Onboard Equipment Vulnerability Analysis
Analyzes security weaknesses of critical onboard equipment
and maps potential attacker infiltration paths.
MG Integration — OT × TI Cross Analysis
Cross-analyzes external threat intelligence (TI) with internal vessel status (OT)
to clearly distinguish between mechanical failures and external cyberattacks.
Threat Intelligence Operations Process
Threat Data Collection
Automatically collects maritime industry-targeted threat intelligence 24/7
from dark web, deep web, open source, and global threat feeds.
Maritime-Specific Analysis & Classification
Analyzes collected data within maritime domain context
and classifies risk levels per shipping line, vessel, and equipment.
MG Integration & Cross Analysis
Cross-analyzes external threat intelligence with onboard OT status data
to clearly distinguish between faults and attacks, and contextualize threats.
Customized Alerts & Report Generation
Issues customized threat alerts per shipping line
and auto-generates IACS UR E26-compliant threat analysis reports.
Expected Impact
instead of post-incident response
threat analysis reports
from equipment vendors to shipping lines
Start Your Threat Intelligence
From dark web monitoring to customized threat briefings — see maritime-specific CTI in action.
