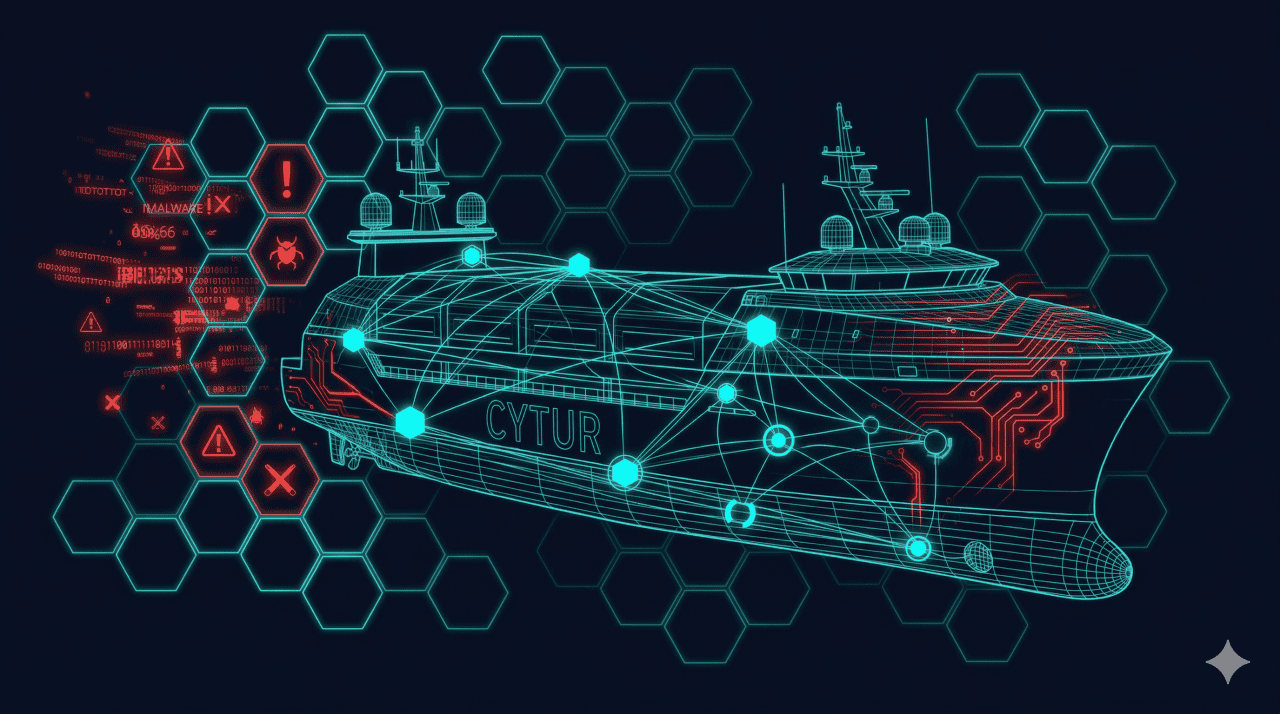
Block Threats
at the Design Stage
Security flaws found after construction cost 10x more to fix.
CYTUR automatically analyzes vessel networks at the design stage,
identifying vulnerabilities proactively through simulated attack scenarios.
Without Threat Modeling at Design,
You're Building Vulnerabilities into the Ship's DNA
Most vessels still treat cybersecurity as an afterthought.
Without security consideration at the design stage, fixing flaws
discovered after construction demands enormous cost and time.
IACS UR E26/E27 regulations require cybersecurity to be embedded
from the design phase — failure to comply makes class certification impossible.
vs. design-stage prevention cost
Design Phase Solutions
Threat Modeler
Digital Security Design Tool for Ships
Creates a virtual network map based on ship design data
and simulates how cyberattacks could infiltrate through various paths.
Attack Surface Analyzer
Maritime Cyber Attack Surface Analysis
Proactively identifies potential security vulnerabilities in onboard asset
software and firmware. Uses Bayesian networks
to predict even unknown threats.
Ship Equipment Cybersecurity Compliance Assessment System
CBS Asset & System Management
Manages all CBS assets installed on vessels in a unified system.
Establishes vendor equipment security verification frameworks,
unifying asset inventories and security status from design to delivery.
Threat Intelligence
Design Phase Application
Pre-installation Equipment Exposure Check
Verifies external exposure vulnerabilities of planned equipment
before installation, supporting update or replacement decisions.
Design Phase Security Process
Equipment Intelligence Pre-check
TI verifies CVE and dark web exposure of planned equipment,
enabling replacement or remediation decisions for high-risk items.
Threat Modeling & Network Design
TM generates a virtual network map from ship design data
and simulates zone-by-zone attack propagation paths.
Attack Surface Analysis & Threat Prediction
ASA analyzes the attack surface per CBS equipment,
with Bayesian AI predicting threat probabilities to prioritize response items.
Unified Asset Management & Documentation
SCS centralizes all CBS asset management
and auto-generates IACS UR E26/E27 compliance documentation.
Expected Impact
saves 10x in post-build remediation
documentation streamline audits
strengthen fleet-wide incident response
Start Securing the Design Phase
See how to embed security from the design stage with a personalized demo.
